Posts
Cybersecurity stuff and things :)°°°
2026
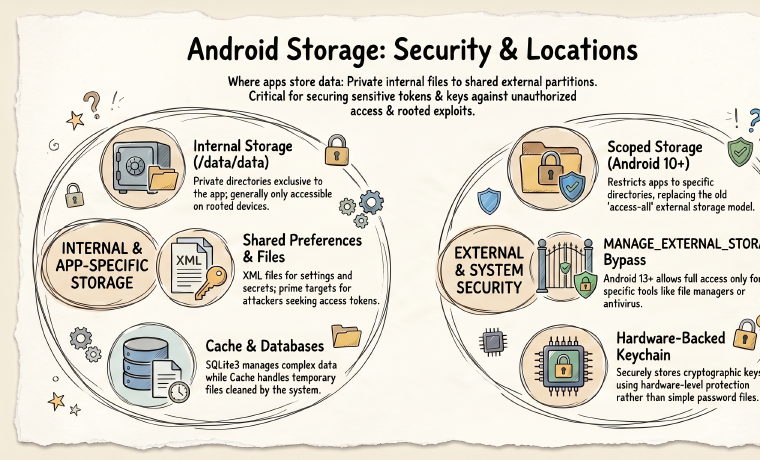
Insecure Storage in Android
A beginner-friendly overview of Android storage locations and what pentesters should look for in each one.
8ksec - AndroPseudoProtect: Ultimate Device Security
Exploiting Android IPC vulnerabilities
8kSec - Factsdroid WriteUp
Android MITM attack using Burp Suite
Android Pentesting with AndroGoat
Android Pentesting To sharpen my skills, I recently took a deep dive into AndroGoat—a deliberately insecure Android application designed to showcase the most common OWASP Mobile Top 10 vulnerabilities. In this post, I’ll walk through how I …
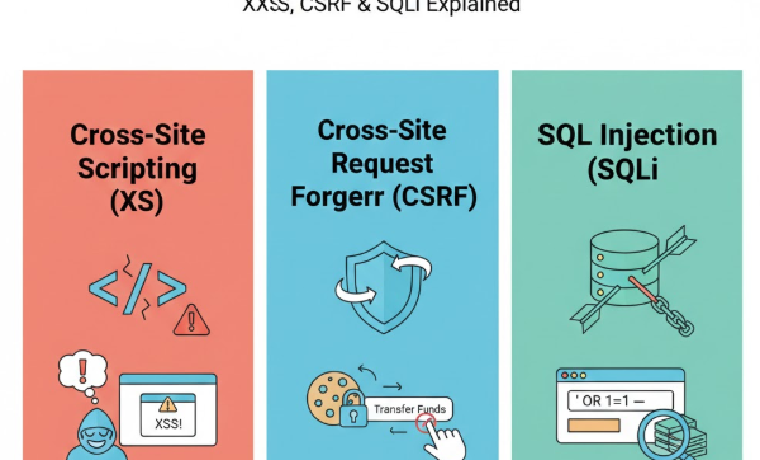
3 Critical Database Security Threats You Need to Know
3 Critical Database Command Injection Security Threats For software engineers, it may be easy to assume that no hacker would target our app since it isn’t big or well known. This attitude can lead to recklessness and lower measures for …
2025

Secure Programming in C: Buffer Overwrites and Overflows
The objective of this lab is to build on our understanding of secure programming in C by analyzing, enhancing, and securing the functionality of the program from Project Lab 1, with a focus on identifying and mitigating vulnerabilities and …
Optimizing your Ruby on Rails app for improved performance and reduced memory footprint
Users desire apps that run smoothly, load fast, and don’t crash. But what determines an app’s performance? There are two key factors: performance and memory usage. Performance refers to how fast your app loads for users. Memory footprint is …
2024
Secure Programming in C: Buffer Overwrites and Overflows
This lab focuses on identifying vulnerabilities in the source code, applying and validating patches, and proposing future best practices to prevent similar issues.
Reverse Engineering
Decompiling and analyzing binaries with Ghidra; examples and notes.
2023
Getting Started With GET Curl Commands
Introduction to curl A curl command is a tool used on the terminal to make network requests using various protocols. curl is designed to aid with the data transfer to and from a server without the need for a web browser. With curl ,you …
2022

Rails Excessive Data Exposure
For software engineers, it may be easy to assume that no hacker would target our app since it isn’t big or well known. This attitude can lead to recklessness and lower measures for securing data on an app. However, it’s important to …